Email (electronic mail) is a form of instant message delivery. You type a message, address it, and send it to the recipient. We use email daily, but we usually do not understand how it works.
Email History
The first versions of electronic mail date back to the 1960's, based on mainframe computers. Back then, there would typically be one large computer, and users would access them from "dumb terminals" (a monitor and keyboard), sometimes remotely. Messages could be shared between different users on the same computer.
Shortly after the Internet was created, Ray Tomlinson made a network-based email system, using the "at mark," @, to separate the name of the person and the name of the computer.
Just as the spreadsheet program VisiCalc would later become the killer app which made PCs commonplace, email was also considered a killer app, making use of the Internet more popular.
How Does Email Work?
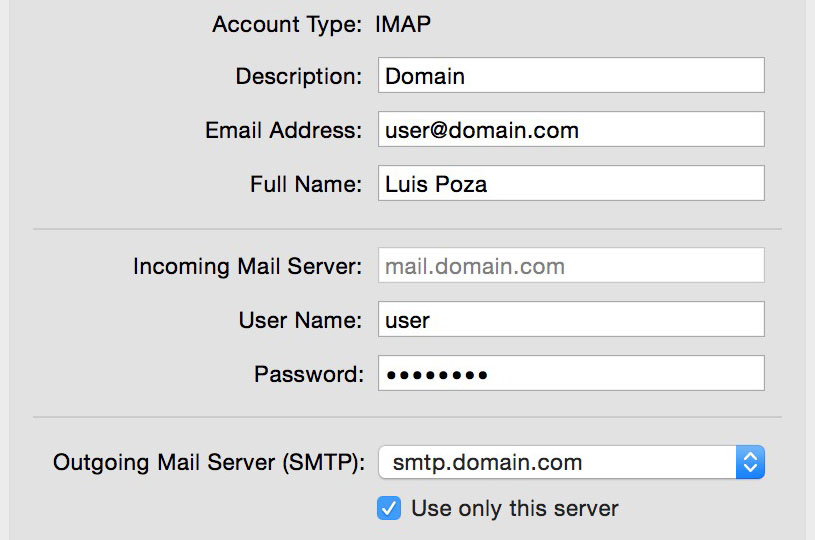
Email is actually two systems: outgoing and incoming email. The two systems are, of course, linked, but different protocols and servers are used for each system.
Outgoing mail is sent using an outgoing mail server, using the SMTP protocol. SMTP servers are like public mailboxes, some allowing almost any sender to use them. SMTP, or outgoing mail servers usually have an address such as smtp.domain.com or the more general mail.domain.com.
Incoming mail is delivered by an incoming mail server, usually using the POP or IMAP protocols. These servers, more like home mailboxes, are the specific location for email accounts; whenever email addressed to a specific account is sent, it is received by the incoming mail server and is stored there until the user accesses them. Incoming mail servers usually have an address such as pop.domain.com, imap.domain.com, or the more general mail.domain.com.

When an email is sent, it goes to an outgoing (SMTP) server. It then locates the destination (incoming) server at the domain name in the address, and send it to that server. The incoming server then holds the email until the account owner logs in and check their mail. The account user might use the POP or IMAP protocols to access the email.
What Is the Difference between POP and IMAP?
From your perspective, the differences may not be very important. For example, POP accounts are simpler, and can only allow one user to connect to the maibox at one time. IMAP is more complex, and allows for multiple users to connect at the same time.
There are a few significant differences, however. The POP protocol downloads the email from the server and saves it on the user's computer, using an email client program, such as Outlook or Apple's Mail app. The server mostly just acts as a temporary storage area.
By default, POP will erase the message from the server when it is downloaded, so it is permanently stored only on the user's computer. This has some advantages, such as quick offline access and searching, but it means that you must always have access to that one computer.
Deleting mail from the server is not required, however; the email can be left on the server for a set period of time before erasure, or never erased from the server at all. This could allow access from another computer, but it would require having a client email app and downloading the email multiple times. If you change the status of a downloaded email on one machine, it will not change on any other machine.
The IMAP protocol, in comparison, leaves the email on the server. Folders can be created to organize mail, and mail can be tagged as "read," "unread," "flagged," or something else. The account's mail can be searched using the IMAP server. In short, it is like having the mail program on the server instead of on your computer. A big advantage is that you can log into the email account from any computer and access all of your mail; any changes you make will be visible on any other computer which logs in.
Client Mail and Webmail
An email client program is a program located on a user's computer which connects to an incoming email server to collect mail using either the POP or IMAP protocol. Typically, the client will store the email locally, on the user's computer. If it is using the POP protocol, it might erase the email from the server.
Webmail uses the IMAP protocol and allows account owners to access their email using a browser interface. The email stays on the server, and can be accessed from any computer connected to the Internet. Most webmail services include the ability to download mail to a client program in addition, using the POP or IMAP protocols.
Webmail began to appear in the mid-1990's as a free service, provided by various companies. Hotmail, now called Outlook, began in 1996; Yahoo Mail in 1997; Gmail in 2004.
Account Full: Delete Email!
A major problem with webmail for the first decade or so was storage capacity. Even as late as 2004, most webmail accounts had a storage limit of 2MB to 4MB. One could get a 10MB or larger account, but it usually cost an annual fee.
As you might imagine, webmail storage could very easily fill up. When it did, the account simply stopped working, and people trying to send mail to it would get error messages. As a result, users had to constantly watch their email storage and delete messages on a regular basis. If you sent someone a large attachment, it could make their email account stop!
This changed in 2004, when Gmail came out and offered 1GB of storage space to all users. Although it was an invitation-only service at first, it quickly became popular, and soon was made fully public. Other services soon began to offer similarly large storage amounts. Currently, Gmail offers 15GB of storage to normal users, and 30GB to educational users.
Pros and Cons
Webmail Advantages:
- can be accessed from any computer or mobile device
- reliable storage; data loss rare
- does not take up space on your devices
- it is free, easy to set up, and easy to use
- usually allows client access as well
Webmail Disadvantages:
- you must be connected to the Internet to use it
- access and use is slower than with a client app
- usually has advertisements, some based on your email content
- can only check email within its own system; Gmail cannot check Hotmail accounts
- can only search email within its own system
Client Mail Advantages:
- it is very fast
- can check multiple accounts all at once, including webmail accounts
- no browser login required; can run all the time and alert you to emails as they arrive
- can quickly search all email stored in all accounts in one search
- storage is limited only by your local storage
- your email address can more easily use your own domain name
- can browse, search, and compose email when not connected to the Internet
Client Mail Disadvantages:
- all mail is stored on a single computer
- the computer could be damaged or lost; without backup, all emails could be lost
- accounts can be hard to set up, and connection problems can be difficult to repair
- Some ISPs block outgoing client email unless a special outgoing server is used, meaning that a portable computer might have to change SMTP servers a few times a day.
Attachments
When you send an email, you often will want to include a file or a set of files. These are sent as attachments. Every email setup should have an option for attachments. Usually, you click a button, are asked to select a file using a navigation dialog box, and then you attach the file. Using an email client, you can usually drag and drop icons directly into the "compose email" window, or else copy and paste objects directly; this is usually not possible using web mail.
Attachments can either be viewed "inline" or separately. "Inline" attachments appear within the email text, either as photographs, PDF files, or icons which launch documents. Inline attachments can often be dragged and dropped onto the Desktop or into folders for saving.

Beware of Malware! Attachments can be an attack on your computer. Especially using Windows, you must never open an attachment unless you are CERTAIN that it is safe. Even if the email seems to come from a friend, you must be VERY cautious.
Know Your Filename Extensions! Look at the filename extension for the attachment. If the extension is .exe, .zip, .bat, .vbs, .pif, or .src, you should be especially careful, although other extensions can be malware also.
Only Open Safe Attachments! How do you know if it's safe?
First, it must be EXPECTED. In other words, the sender told you they would send it. If you receive an attachment that you did not know about previously, then it is probably a virus.
Second, it should be in a specific email—that is, the email message must have a message clearly written to you, and should make reference to a specific event or project the attachment is related to. DO NOT open attachments where the message just says "look at this!" or "very funny!" or "photos from the party." The message must be specific, for example, "Luis: This is the PDF of the schedule that you asked for two days ago at the meeting."
A very common form of malware received by email will open a victim's address book and send a copy to everyone on the list. The recipients, seeing the email as coming from a friend, will more often open the attachment.
It is important to know filename extensions! When you get an email, sometimes it has attachments. These attachments often contain malware (e.g., viruses), especially when they have certain filename extensions.
Filename extensions you should be very cautious about opening include:
- .exe
- .zip
- .scr
- .bat
- .pif



